UKTIN spoke to Dave Happy and Dr. Greig Paul, Chair and Vice Chair of UKTIN’s Security Expert Working Group to learn more about its Future Capability Paper, which was published today. You can find more information on the future capability paper series here.
If you’ve not yet seen the previously published papers, you can find the Wireless Networking paper here and the AI paper here.
Read the Security Future Capability Paper
Please talk us through the process of creating the paper.
We set out to produce a report explaining the current status of security today. This started with a series of discussions, predominantly focused on the current challenges in security, not only in technology but also policy. A second recommendation paper is planned for later in 2024.
We were very pleased with the huge amount of support we received from our EWG members. The group has done a fantastic job; everybody was willing to go that extra mile. We are fortunate to have a great breadth of knowledge in the group, and each member had a different, unique perspective to bring to the topic, including specialisms in IT networks, policy, cloud, regulation and infrastructure. One member is a former post-graduate student who has worked with us on other programmes. Diversity is a good thing and our group welcomes people of any age from any background – so long as they want to contribute. Everybody did.
What is the one thing you’d like people to know about the report?
We would like to stress that this is an independent report. We are volunteers and the conclusions are based on what we have seen. This may not be what other people see. This is our sector and our expertise. The report includes what we consider to be the most important factors today within security in the UK.
It is also important to note that security is different in that it is a cross-cutting topic and it reaches into other domains too. The security of networks is fundamentally driven by the standards and norms of what we deploy. What we have found is there are solutions to the recurring problems. Most of the barriers to adoption are not technical, but more related to business models, incentives and culture. To solve these issues, we need to focus beyond simple R&D, for example, on skills and the next generation of talent. Only then will the sector truly thrive sustainably.
What surprised you most while preparing this report?
We noticed that human error was the biggest problem, not machines. It is not necessarily just a research question therefore, but a consideration of the value of research if we as humans still can’t or won’t do what is required to improve the basic level of security. This is not just a UK problem. In addition, the problems we are facing in telecoms are similar to those facing the IT world. We expected this to happen, but the extent to which the same solutions exist has been quite surprising. Adoption is the main challenge. The measure of success will be if we can make our products harder to breach and more resilient. But how do we drive that action?
What surprised us the most was the importance of standards in the process. If you’re running an internet-based infrastructure, for the internet to work globally we still have to dine with other countries who perhaps don’t share our democratic views. We still have to agree on standards for technical security. We had initially not grasped the fundamental significance of standards to security.
There was a broad sense of agreement between us. As the report was being prepared, everybody was chipping in. The number of people who have made contributions has been humbling. This is a highly engaged group and we are lucky to have them!
What conclusions were you able to draw?
There is significant room for improvement. We need to take our own medicine here. We can do all the R&D in the world, but if humans aren’t ready to adopt, nothing will change. We also need to consider how to fund R&D and security: for example, access to investor capital, commercial-funded R&D and so on. Ultimately, there is a lot of interesting R&D that is not reaching the market, which is evidenced in the paper. What are the outcomes we desire? How do we make systems more secure?
It appears too that we are going to need to shift the balance between pure and applied research if expectations are to be met. Applied is defined as a more immediate industry-focused need, something that can be more readily commercialised. If we’re doing more applied research, does that in turn mean that we should be more focused on industry and standards and how we spend R&D budget? Very probably yes. Both pure and applied research are of considerable value and both are needed but where there is a clear objective to be achieved, we may need to make decisions about how to spend accordingly.
Alongside this, the skills gap also needs to be addressed.
It is important to stress however that all of the problems we identified can be addressed.
Are there any themes picked up in the security paper that have been featured in the other EWG papers?
Our first paper is a situation report. Our second paper will be about the conclusions we can draw based on this evidence. We held an event on the 20th of March, where we invited attendees to share their thoughts about our findings, what their conclusions were, and what recommendations they felt could be included in our next paper.
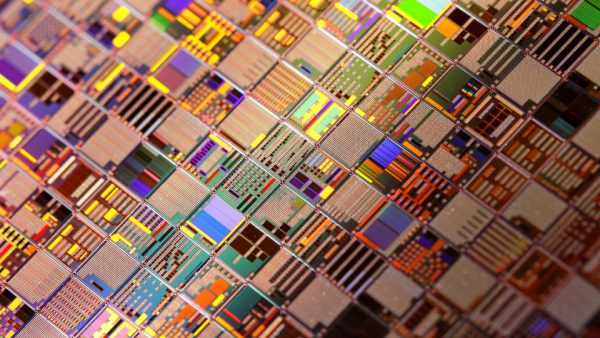
As we stated earlier, security is a cross-cutting topic. It sits in the inboxes of every EWG. We have worked closely with the AI EWG for instance, and contributed our views into their work for their recently published Future Capability Paper. We have also worked with the semiconductors team and contributed to the skills discussion.
It’s great to see conversations starting to grow between the EWGs. We are here to help everybody and anybody who would like us to help. We are conscious of our responsibility.